
CONGRATULATIONS!! YOU’VE WON…possibly.
You’ve just received the two letters above. Which one gets read further and which one goes straight into the trash?
Congratulations! You are eligible to win a dream vacation.
Congratulations! You have won a dream vacation.
Thanks to the advertising & sweepstakes industry we’ve learnt from a very early age that while the two sound like they’re saying the same thing, they are, for all intents & purposes, actually quite the opposite of each other. ‘Eligible to win’ means that you could win a vacation, but you haven’t won it yet and you’ll need to complete some additional actions. ‘Have won’ on the other hand means you have already won the vacation and you don’t need to do anything else except go enjoy your time in the sun.
So, what does this have to do with AWS and more specifically with your PCI-DSS (Payment Card Industry Data Security Standard) compliance?
Let me first be very clear on what I am not saying. I am not saying that the AWS claims of PCI-DSS compliance are false or that they are meant to mislead you in some way.
At the time of writing, AWS is certified as a PCI-DSS 3.2 Level 1 Service Provider, the highest level of PCI-DSS compliance possible, and has over 90+ of their services in scope. Sounds impressive doesn’t it? Well, to put it simply, it really is!
Anyone that has been through the PCI-DSS audit process will know how much work is needed to prepare for the initial audit and how much additional work is then needed to maintain that level for the next 365 days to pass the annual re-audit.
At NeosIT, we’ve built 2 PCI-DSS 3.2 Level 1 Service provider certified environments from scratch for our on-premises hosting environments and while these didn’t have anything near the 90+ scoped services that AWS has, it still involved a staggering amount of work.
So if AWS is already certified then where’s the problem?
If you need PCI compliancy for your application, then why go through all the pain of doing it yourself when you could simply deploy it in AWS and be done with it. Right? Unfortunately, not!
This brings us to what I am trying to say and that is that many application owners misunderstand what exactly an AWS PCI compliant service means to them.
We have encountered this same misunderstanding when engaging with customers for both our on-premises PCI environments and those interested in AWS PCI environments.
Simply dropping a workload onto a PCI certified service does not necessarily make your application PCI compliant!
The simplest way we have found to explain this concept to our customers is to consider the AWS services as PCI eligible rather than PCI compliant when it comes to their workloads.
‘PCI eligible’ means that your workloads could be complaint on AWS, but they aren’t compliant yet and you’ll need to complete some additional actions.
Ultimately, when it comes to getting your application certified, you are responsible for the PCI compliance of all components that make up your application environment. That includes everything from the code that your application is built on to the access controls on the doors to the datacenter in which it is hosted.
For your application to be compliant, all underlying components need to be compliant and if, for example, your application runs on physical hosts that are not compliant then your application will most likely not be certified.
Now, as AWS already has certified some of these underlying components, you do not have to worry about these lower layers being compliant. If you run your application on those certified components then your application could get certified… but only if you make sure that the components that you are responsible for also meet the requirements!
In essence your application is PCI eligible if it runs on AWS PCI compliant services. It could be PCI certified, but it’s not compliant yet and you’ll need to complete some actions before it is certified. Consider the following simplified example:
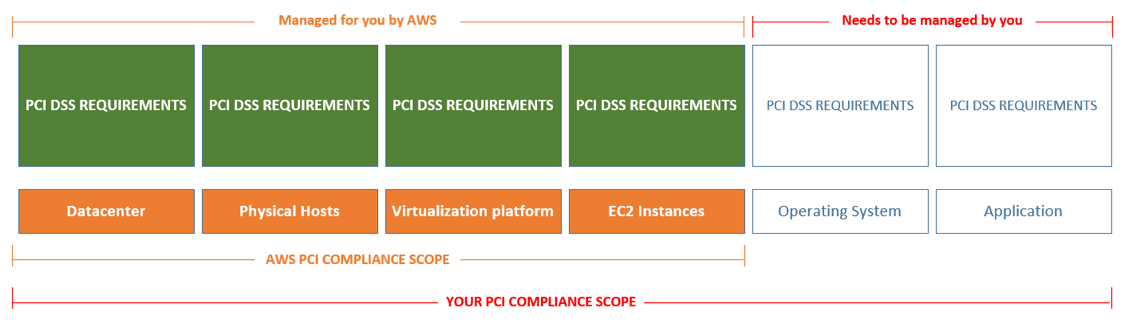
AWS EC2 is a PCI compliant service
That means that all the layers below and including the EC2 instances are already compliant.
If your application runs on top of these compliant layers you wouldn’t need to worry about lower level things like ‘Do the datacenter doors have video cameras?’, BUT you would still need to fulfill the PCI-DSS requirements for the Operating System & your Application running on that EC2 instance before you can be certified as compliant.
This would mean taking care of things like:
- Regular security patching.
- Anti-Virus is implemented.
- Encryption (transit & rest) is implemented.
- Security logs are collected.
- File integrity monitoring is implemented.
- Access controls are implemented.
- Network ports are restricted.
- Vulnerability scanning is done regularly.
- Penetration testing is done regularly.
- ...
Now that might not sound too bad and having AWS take care of a large chunk of your PCI requirements does definitely help make your life easier.
However, when you dive a bit deeper into the PCI DSS requirements, you quickly figure out that, while there only 12 main PCI requirements to be fulfilled, each of these main requirements actually consists of multiple ‘sub-requirements’ which in turn also consist of ‘sub-sub-requirements’ which brings the actual number of requirements to be fulfilled to over 200…and these need to be fulfilled for every applicable component in your stack!
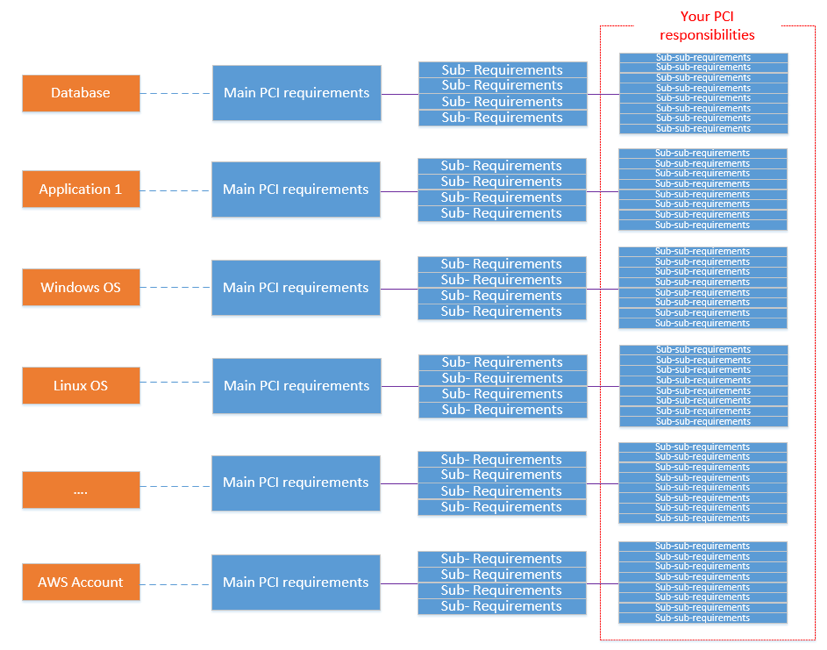
This is normally where most customers start looking at higher level service models (i.e. moving from an IaaS model to a PaaS model) or at Managed Service Partners to whom they can offload these responsibilities to and rather spend their time focusing on their core business.
The big concern with choosing these options is usually the increased cost of the solution, however there is a very strong case to be made that going it alone works out more expensive! This is especially true if your organization is unfamiliar with PCI or don’t have the specialized people required. However that is a topic in itself and best covered in a separate article.
If you have any additional questions about simplifying your PCI certification process or are planning on migrating from an on-premises solution to the cloud and have concerns, then we would be happy to hear from you.
Simply drop us a mail at info@NeosIT.com.



